Anastasiia Voitova breaks down the major security and privacy announcements from WWDC
Last week, before WWDC began, I interviewed Anastasiia Voitova about her expectations for the event from a security and privacy perspective — and in this guest article, she shares her list of the major security-related announcements so far — her thoughts on them, and her tips on what session videos to look out for throughout the week.
Security and privacy are two topics that are incredibly important to Apple and their platforms, so naturally they’re very much in focus during this year’s WWDC as well.
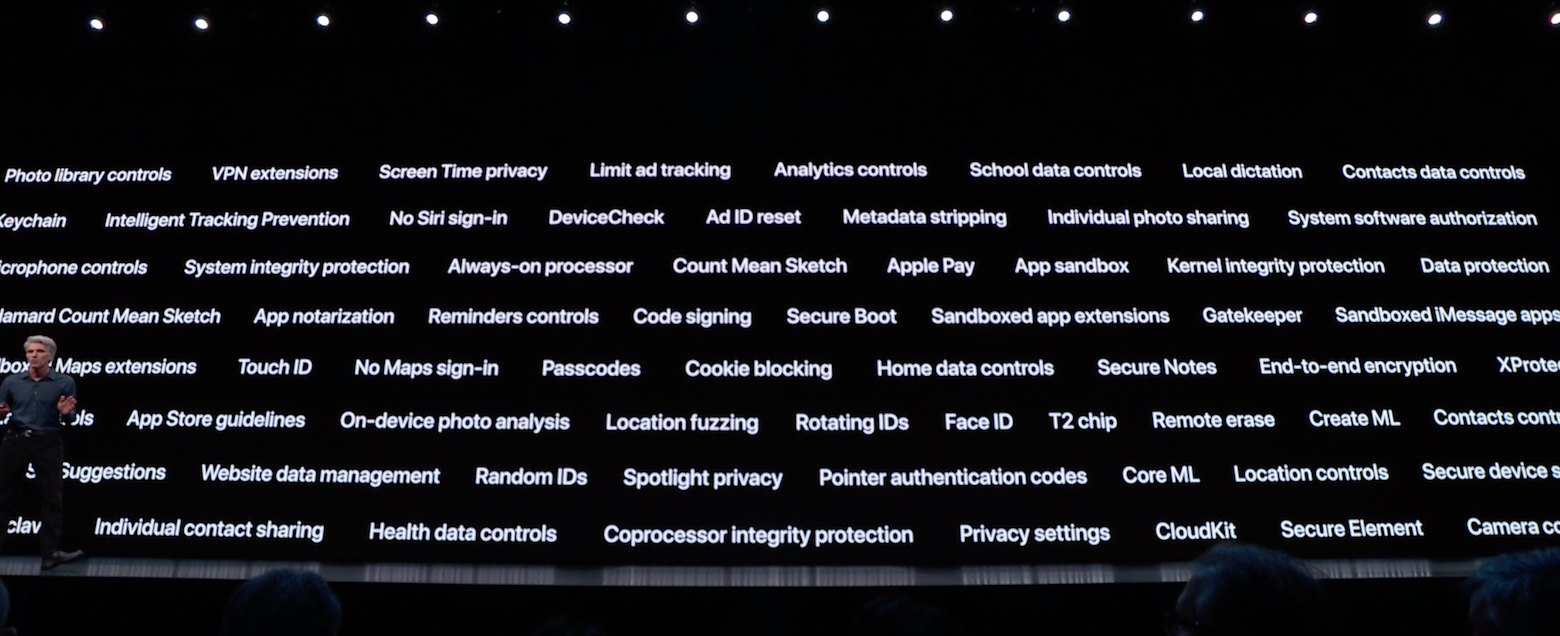
A few of Apple’s new security and privacy features announced this year (source: Apple)
Let’s go through some of the major security and privacy-related announcements and what they might mean for both users and developers.
watchOS announcements
The new Noise application on watchOS allows you to measure the noise level around you, to understand if it’s harmful to your ears, but the Watch does not record all of the sound — samples only — and doesn’t save your audio anywhere.
Apple Watch will now also collect even more health data itself, but no worries, Apple says that data is fully encrypted on-device, completely under your control. Finally, watchOS will now also support independent apps, which is cool, but the question is whether these apps’ network connections will be forced to use TLS through App Transport Security?
Sign in with Apple
Every time a user uses “Sign in with Facebook” or “Sign in with Google”, they make their life a bit easier by ”paying” with their personal data (because social networks can link their account to their in-app behaivor, interests, etc.). But soon people will be able to use “Sign in with Apple” instead, to log in to applications using FaceID or TouchID, without compromising any personal information.
Moreover, if an application asks for the user’s email, Apple can generate a unique random “virtual email box” for each application, and redirect emails from it to the user’s real email inbox. Easy to use, easy to stop using.
The most important news, however, is that Apple seems to be requiring all apps that currently support sign in with social networks to adopt “Sign in with Apple” later this year. In an update to their App Store Review Guidelines, Apple writes:
”Sign In with Apple will be available for beta testing this summer. It will be required as an option for users in apps that support third-party sign-in when it is commercially available later this year.”
HomeKit
Videos from home security cameras can now be stored securely in iCloud, end-to-end encrypted. Storing them is free with each iCloud account and won't count against storage plan limits.
Further improving users’ home security and protecting the networked infrastructure within homes — select routers will soon receive a “HomeKit firmware update”, basically acting as a firewall/VPN, to shield home networks from connected “smart devices”.
The Verge reports that “Linksys, Eero, and Spectrum will initially support the HomeKit features”, in regards to which router brands that will receive this update first.
Location services and Find My
Users will now be able to allow apps to access their location just once, preventing misuse, since the next time some “nasty app” wants to read the user’s current location — it’ll need to ask for permission again. Moreover, Apple will now make it more complicated to use indirect ways to retrieve location using WiFi or Bluetooth.
Also, here’s an interesting change as to how location permissions are granted, as spotted by Gui Rambo:
“Apps can’t ask for ‘always’ location permission by default anymore. Users are prompted when the app actually tries to use location in the background.”
Speaking of location — soon, if you misplaced your Mac, even if it doesn't have a WiFi connection — it will now send chunks of data via Bluetooth, allowing other Apple devices to locate it. Apple states that “All data sent is encrypted and anonymized”, and this article by Matthew Green goes into more detail explaining cryptography layer and the potential security concerns with this new system, and how Apple seems to be working around them.
Other user-facing privacy and security announcements
Here’s a few other notable user-facing privacy and security-related announcements that we’ve seen from Apple this week:
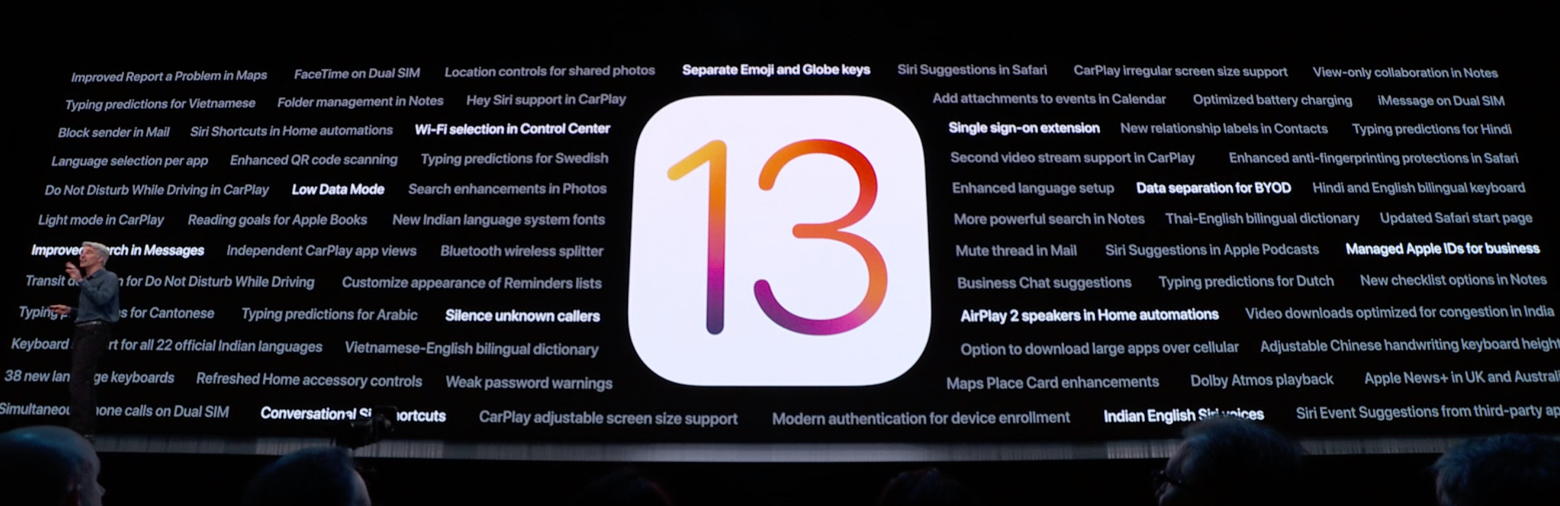
Some of iOS 13’s new security and privacy-related features (source: Apple)
There’s a new single sign on extension for enterprise apps.
Users can now use separate iCloud accounts for personal and work-related purposes, improving the “separation of concerns” between the two, and avoiding mixing things up.
Voice Control is an accessibility enhancement for iOS and macOS, allowing users to control their devices verbally. Apple says that all voice processing is being made on-device, locally, and that the data is not being sent to Apple.
You can now double-click the side button of your Apple Watch to authenticate on your Mac (for example to unlock a locked note, or to approve app installations).
If you’re developing security software, then I recommend that you check out the new EndpointSecurity framework, which allows system events to be monitored for potentially malicious activity.
App Store review guidelines
WWDC has also brought with it a few updates to the App Store review guidelines, mostly focused on data security and privacy. As I predicted in the interview I did with John last week, Apple is pushing developers into a ”GDPR kind of direction”.
Some of the highlights include:
Guideline 5.1.3(i): Apps may use a user’s health or fitness data to provide a benefit directly to that user, such as a reduced insurance premium, if the app is submitted by the entity providing the benefit and the data is not shared with a third party. The developer must also disclose to the user the specific health data collected from the device.
Guideline 5.1.1(vii) (New): Apps that compile information from any source that is not directly from the user or without the user’s explicit consent, even public databases, are not permitted on the App Store.
Guideline 5.1.1(i): Apps must get consent for data collection, even if the data is considered anonymous at the time of or immediately following collection.
I’ve had numerous discussions with people on Twitter during the past few days about the 5.1.1(vii) clause. The questions are — how is Apple supposed to check for that during app review, what exact databases are we talking about, and where will the lines be drawn?
We’ll most likely find out more about that soon, but in the meantime, you can read the full App Store review guidelines update here.
CryptoKit
Apple’s new CryptoKit framework lets you write less code (and better code) when it comes to encryption — thanks to its more high-level API. Remember how cumbersome the CommonCrypto API is? Well, with CryptoKit, you only need one line of code to generate symmetric keys, or to encrypt data, or to calculate a secure hash, or to save data to the Secure Enclave. Easier than ever!
I think that CryptoKit’s APIs might be inspired by more modern cryptographic libraries, like libsodium or Themis, which is great.
CryptoKit also makes a new suite of ciphers publicly available. For example, AES GCM is now available as part of the public API. Chacha20-Poly1305 is currently in beta, but I hope it will be made completely public with the final release of iOS 13. I again predicted these changes in my interview with John, so I’m really happy to see this happening.
CryptoKit also marks hash functions like MD5 and SHA1 as ”Insecure”. That means that developers can still use them for backward compatibility — but Apple is following modern crypto-coding best practices, and is marking insecure APIs as, well, insecure. Don't use these hash functions for password hashing — it’s much better to use special password hashing functions (like Argon2 or PBKDF2), or to stick to using cryptographic libraries that abstract these details — like Themis — allowing developers to relax.
For more information on CryptoKit, watch Session 709 and play with this playground.
As someone who is writing crypto-related code full-time, I'm very happy with these announcements!
By the way, if you’ll end up using CryptoKit (or any other encryption frameworks) in your app, then don’t forget to declare that your app is using encryption, and submit an annual self-report if needed. More on Apple’s regulations on cryptography.
Security and privacy-related WWDC sessions
Just like previous years, many WWDC sessions are focused on security and privacy-related topics. Here’s my list of sessions to look out for throughout the week:
I plan to watch them all! 😎
To wrap up
Oh, what a WWDC! Of course, I couldn’t mention everything in this article, and I'm sure that during the sessions we’ll get a lot more detailed info.
If you're interested in learning more about cryptography and security, I suggest that you to follow these people (among many other people who are doing great work in this field):
Stay secure, use encryption! 🔐
Thanks a lot to Anastasiia for this great overview of some of the security and privacy-related announcements from WWDC. Make sure to follow her on Twitter (her conference talks about security and encryption are fantastic!). Also let her know if you have any questions or feedback on this article.
